Blog post
Fraudsters are Exploiting the Abandoned Identities of Expats
Charlie Custer
Published
March 25, 2026
We know that fraudsters exploit the abandoned US identities of immigrants who once lived in the United States but have since left the country — this is called Assumed Identity Abuse (AIA).
But what about Americans who renounce their citizenship and leave the country? Much like immigrants who have left the country, these people have effectively abandoned their US identities, but those identities don't disappear. And fraudsters, it turns out, are exploiting that.
When we analyzed a sample of "renounced" identities and compared that to samples of US identities, we found that the renounced identities were significantly more likely to have been exploited for identity theft. Renounced identities were also exploited more often, with a median of roughly 8x more high-risk applications linked to their identities (post-citizenship-renunciation) than were linked to exploited identities in the control groups.
Active exploitation: a sample case
To understand what this type of identity fraud looks like in practice, let's walk through an example. What follows is a real case, although we have changed the name and anonymized other details to protect the victim's privacy:
Tarin Sule was born in 1991, probably somewhere in the area of Washington, D.C. Based on a LinkedIn profile that appears to belong to the same person, he went to a D.C. area college and worked as an intern at a D.C.-based company before taking a full-time role in New York. Several years later, around 2015 or 2016, he appears to have moved to the Middle East, taking a series of jobs in the region and founding a startup based there in 2017.
According to the US Federal Register's lists, he renounced his US citizenship in 2019. And as of 2026, Tarin is still located in the Middle East, according to the LinkedIn profile.
However, in late 2024, Tarin's identity was used in an account-opening application to a major U.S. bank. This application lists Tarin's correct name, DOB, and SSN, but was submitted from a California IP address, with a California phone number, and listing a Southern California mailing address. Tarin has no known history in California. The application also lists what appears to have been a brand-new email address at the time of application. These are classic signs of identity theft, and SentiLink scored this application as high-risk.
In early 2025, the fraudster appears to have tried again, submitting two more applications to the same bank using Tarin's identity in combination with different contact information — another new email, a different Southern California address, and a different California phone. Both of these applications also scored as high-risk.
And it appears the fraudster or fraudsters exploiting Tarin's U.S. identity haven't given up. In late February 2026, two additional applications were submitted in Tarin's name, one to a rent-to-own firm and another to a different major U.S. bank. Again, these applications scored as high-risk for identity theft.
How we linked renounced-citizenship identities to identity theft risk
The U.S. Federal Register publishes quarterly lists of Americans who've chosen to renounce their US citizenship and expatriate. The lists include a first name, last name, and middle name or initials if available, for each individual. No additional identifying information is provided, but since the lists are issued quarterly, we know that the identities included on a given list must have renounced their citizenship before the date the list was issued.
To analyze whether these "renounced" identities are being exploited, we looked at names from the past ~15 years of renunciations and identified a group of 616 renounced identities with very rare surnames (all surnames with fewer than 100 total instances in the 2010 US census).
Because these surnames alone are so rare in the United States, if an application in our database matches the surname and the given name provided by the Federal Register, the application identity and the Federal Register identity are very likely to be the same.
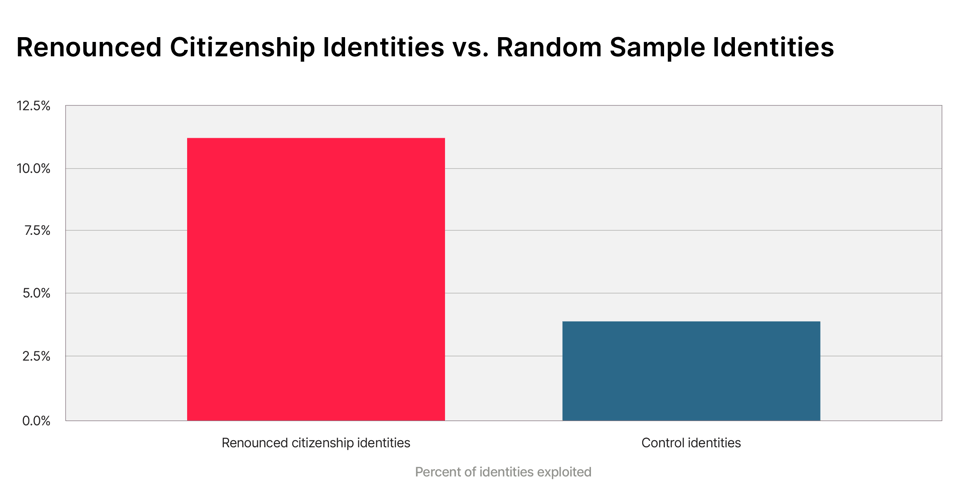
For these 616 identities, we searched our database for bank and credit applications that were submitted after the applicant identity renounced their citizenship and that scored high for identity theft risk with SentiLink's Identity Theft Score. We found that 69 of these identities, or 11.2%, were associated with at least one high-risk identity theft application submitted after they'd renounced their citizenship.
We then compared this to a random sample of roughly 4,000 identities from our database who, like the renounced group, had extremely rare surnames, and found that 3.91% of those identities had been exploited.
That is a dramatic difference. Renounced identities were 2.86x more likely to have been exploited by fraudsters.
These renounced identities were also exploited more often (11.8 high-risk applications on average) than the exploited control identities (1.88 high-risk applications on average).
This fraud M.O. appears to be a small but active subcategory of Assumed Identity Abuse. These renounced identities likely appeal to fraudsters for the same reason they target the identities of immigrants who've left the U.S. — since the victims are no longer in the country and have stopped using their U.S. identity, they are unlikely to ever notice or report that it has been stolen.
Are fraudsters using the Federal Register to find targets?
Manual review of a sample of high-risk applications from the exploited renounced identities suggests that most of these applications include the identity's true date of birth and SSN — information that is not available from the Federal Register.
It is possible that fraudsters are sourcing names from the Federal Register's list and then searching for the rest of the PII elsewhere. But SentiLink researchers have already documented that fraud markets openly sell packages of "expat" and "emigrant with credit history" identities. We think it is more likely that fraudsters are sourcing these identities primarily from markets like these — these packages likely include a mix of identities including immigrants who've left the US, US expats who may one day return, and the identities of people who've renounced their citizenship and moved abroad.
Conclusions
It appears that fraudsters are actively targeting the U.S. identities of anyone who has permanently left the United States, whether they are former immigrants or former citizens. And unfortunately, because the Federal Register publishes only names — the vast majority of which are common enough that multiple people share the same name — there is no realistic way for FIs interested in combating this trend to leverage those lists.
However, these applications are detectable with identity theft tools such as SentiLink's Identity Theft Score. Financial institutions should be particularly alert to applications that show signs of the typical patterns we see in other Assumed Identity Abuse (AIA) cases: identities with an established history in one location, a period of dormancy, and then a burst of new activity, often in a location to which the identity has not previously been tied, and using new phone and/or email addresses.
Learn more about how abandoned identities and abandoned PII elements are used by fraudsters in our latest Fraud Report, which is free and available now.
Also, see how abandoned identities like these become fuel for fraudulent schemes in this CBS news report featuring Dr. David Maimon, SentiLink's Head of Fraud Insights:
Related Content

Blog article
April 14, 2026
The Montana Loophole Is Closing. Are Lenders Holding the Bag?
Read article
Blog article
April 1, 2026
Inside "Pell Running," the Federal Student Aid Fraud Congress Is Trying to Stop
Read article
Blog article
March 30, 2026